Workflow in TaskForce 2
Atola TaskForce 2 provides a complete feature set for forensically sound evidence acquisition process. Based on our own decade-long experience of working with data storage devices and our clients' experience in digital forensics we strongly recommend this workflow:
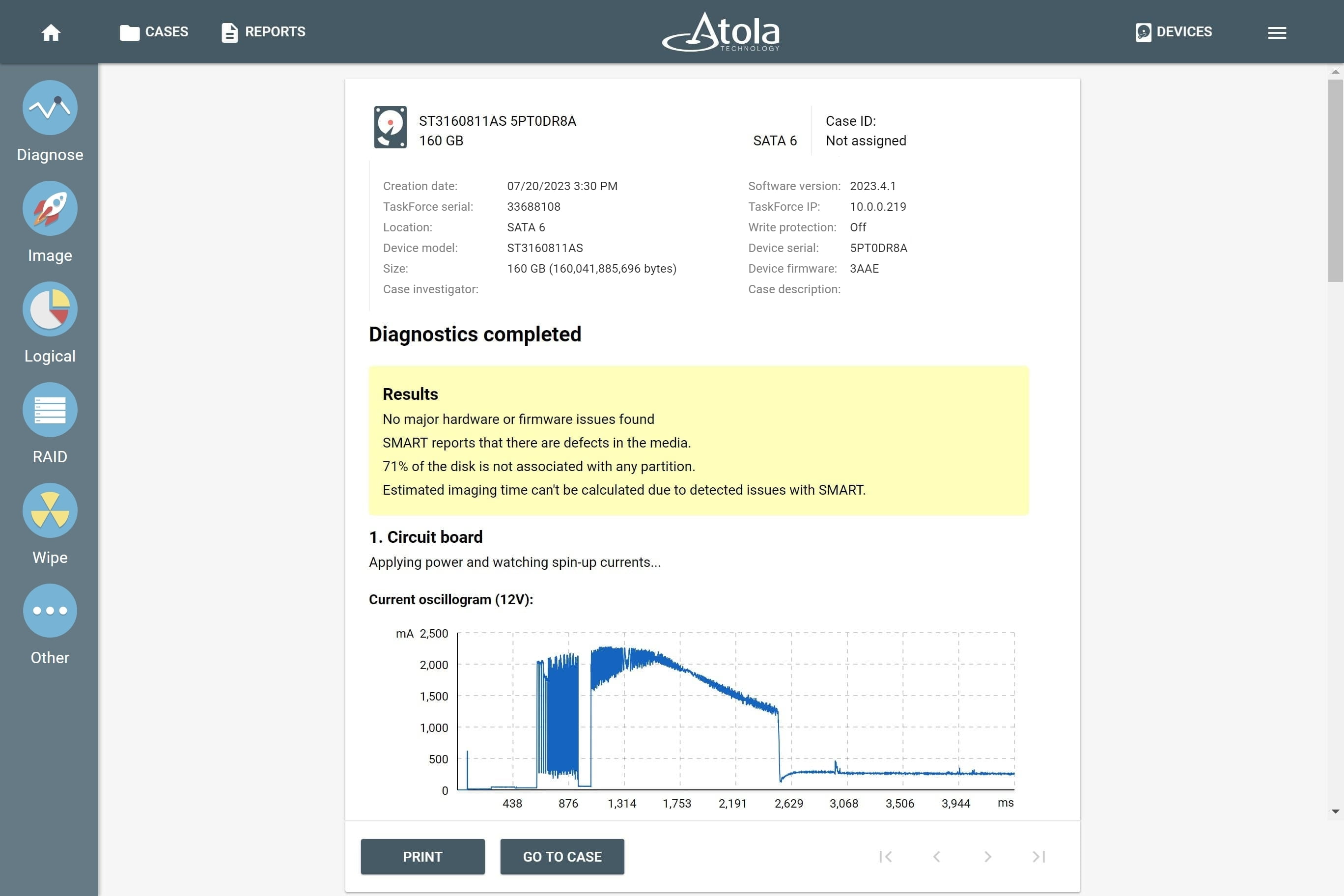
1. Diagnose the drive
TaskForce 2 is equipped with a fully-automated diagnostics module. It diagnoses all hard drive systems:
- Printed circuit board (PCB)
- Head stack
- Media surface
- Firmware
- File systems
After diagnostics finishes, the tool prepares a report and lets you know the exact issue with the drive; it also suggests the next step for optimal data retrieval.
2. Get access to the media
TaskForce 2 detects hidden areas on the drive set via Host Protected Area (HPA) or Device Overlay Configuration (DCO). The system can automatically recover/remove them. To avoid changing the state of the drive, HPA reset until power cycle option is available.
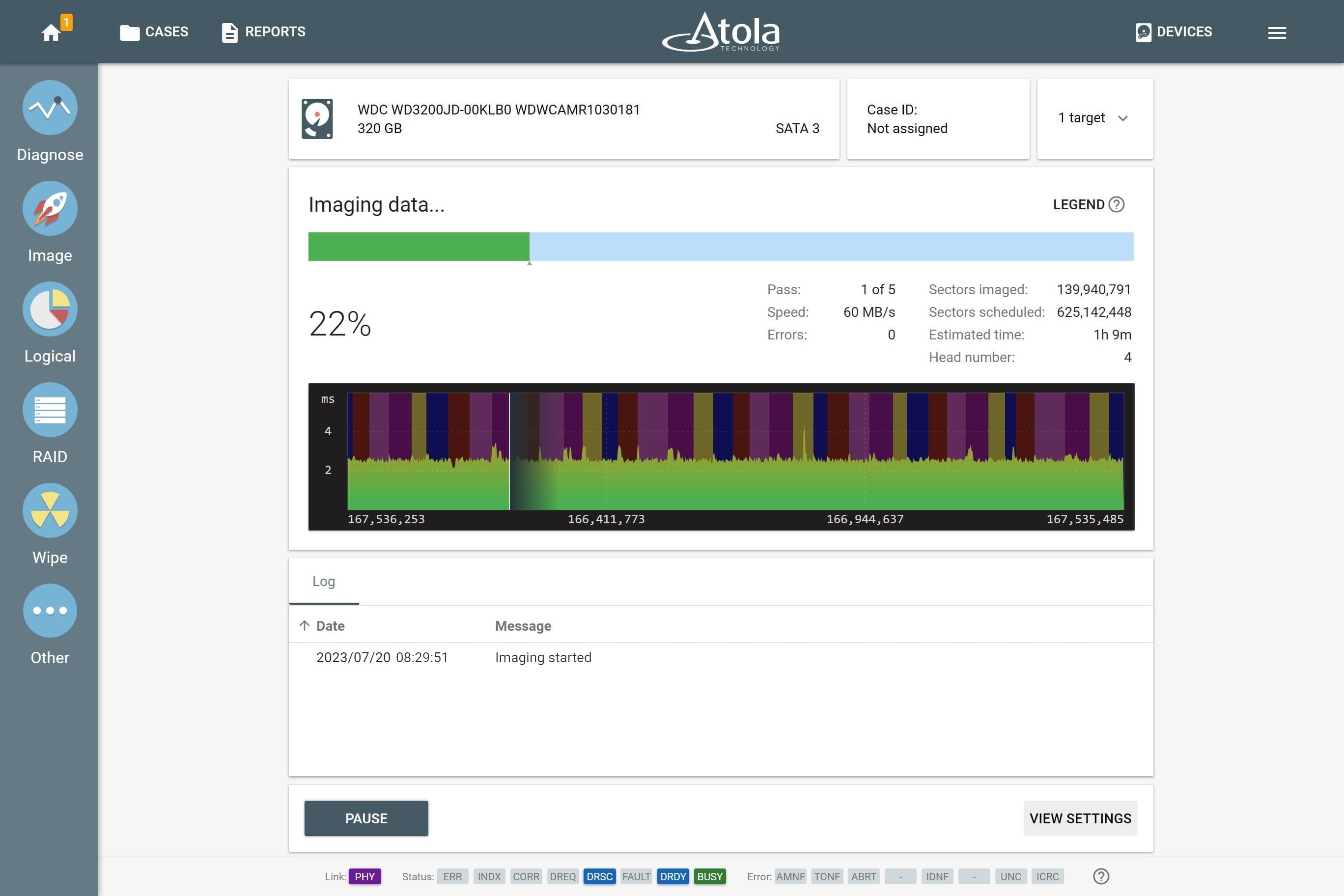
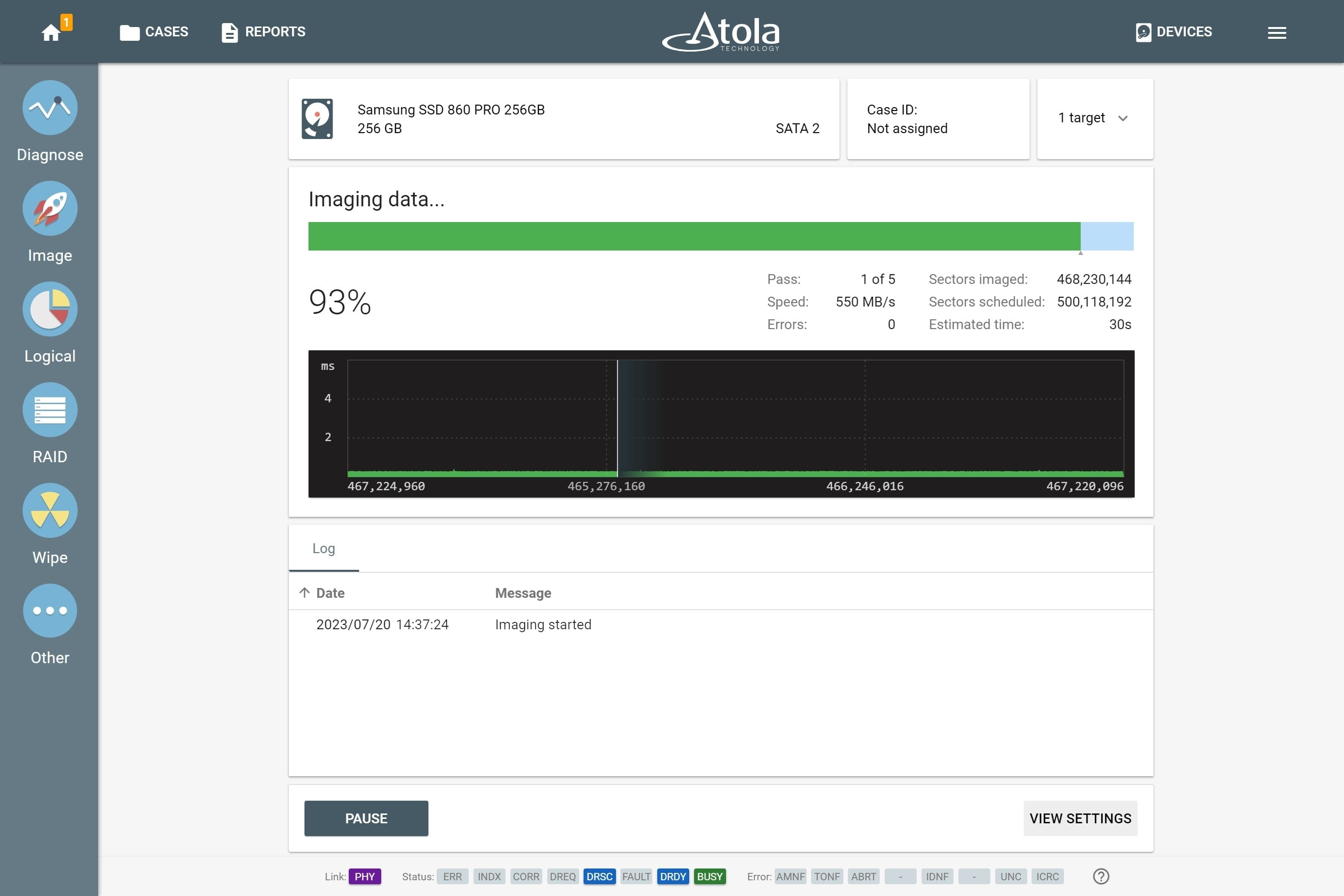
3. Image the evidence
To ensure efficient imaging of both good and damaged drives, TaskForce 2 is equipped with a sophisticated and powerful imaging module. It allows creating a bit-to-bit copy of the evidence. Based on the diagnostics report, image drives with default settings or adjust them if the source evidence is damaged and requires special treatment.
If damaged or degraded head is detected during diagnostics, the imaging module will ask whether the operator wants to disable it when starting the first imaging session.
4. Calculate hash
To verify the the image, calculate hash of both the evidence drive and the image. In the imaging settings, you can enable automatic hash verification (post-hash) of the targets.
With damaged devices, we recommend calculating hash during imaging and using segmented hashing. This way data on a fragile device is only read once, and you avoid further damage to the media.